Don’t hardcode your secrets in Kubernetes manifests, and other container pitfalls to avoid
authentik is an open source Identity Provider that unifies your identity needs into a single platform, replacing Okta, Active Directory, and auth0. Authentik Security is a public benefit company building on top of the open source project.
At the time of writing this post, the downfalls of using YAML as a templating language are being debated on Hacker News. The headache of trying to customize Helm charts is a gripe we share at Authentik, which we’ll get into below.
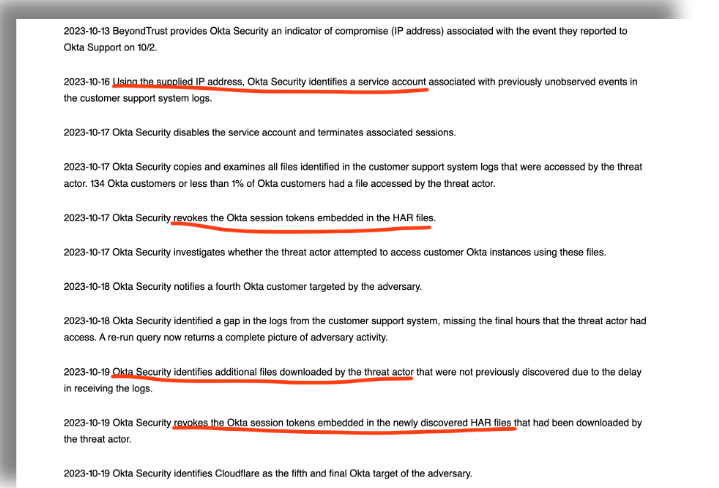
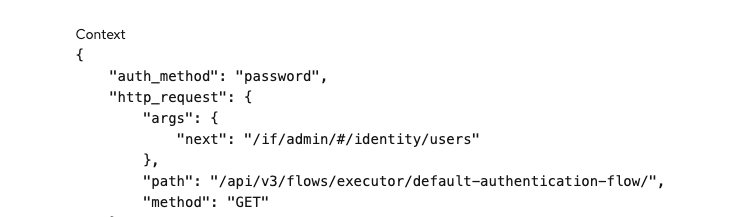
This post is about how we test and deploy authentik using containers, some gotchas we’ve encountered, and lessons we’ve picked up along the way.
When the company founder is from an Infrastructure background, and the first person he decides to hire (that's me!) is also from Infra, you can imagine that we end up with some pretty strong opinions about tools and processes.
This is part of an ongoing series about the tools and products that make up authentik’s stack (you can also read about our infrastructure tooling choices and what’s in our security stack).